In the vast and ever-evolving digital landscape, businesses face a formidable challenge: safeguarding their most precious digital assets from relentless cyber threats. As technology advances at an unprecedented pace, so do the malicious tactics employed by cybercriminals. The sobering truth is that no organization, regardless of size or industry, is immune to the possibility of a devastating breach.
Stakes are higher than ever before because it’s not just about protecting sensitive data or preserving your company’s reputation; it’s about ensuring your business’s very survival.
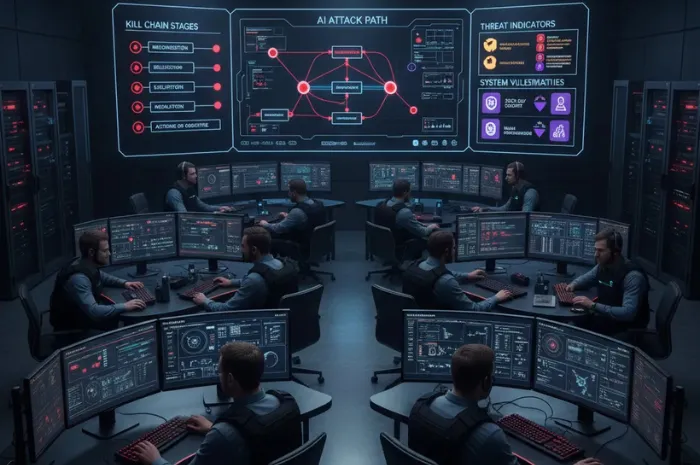
An external cybersecurity agency during their audit runs different types of penetration testing to safeguard your business from financial loss, legal ramifications, and damage to customer trust looming ominously. They can fortify your defenses and help you stay one step ahead of the ever-adapting adversaries.
What is penetration testing?
Penetration testing or pen-testing, often referred to as ethical hacking, is the proactive approach that enables businesses to identify vulnerabilities in their digital infrastructure before cyber criminals do. It is a controlled and systematic attempt where skilled cybersecurity professionals infiltrate systems, networks, and applications, employing the same techniques and tools as employed by real attackers.
These professionals follow standard penetration testing tools, framework, and approaches to secure your cyberspace within ISO/IEC 27032 standard.
Why should businesses heed to penetration testing?
Because the cost of complacency can be exorbitant. A single security breach can lead to irreversible damage, ranging from loss of valuable intellectual property and financial assets to the erosion of customer trust, which is painstakingly built over years of hard work. The truth is, it’s not a question of if your business will be targeted—it’s a question of when.
By conducting regular penetration tests, businesses can:
Identify Vulnerabilities: Different types of penetration testing help discover vulnerabilities and security weaknesses that may exist in their systems, networks, or applications. This allows for timely implementation of appropriate security measures and reduces the risk of successful cyberattacks.
Mitigate Potential Risks: Penetration testing gives valuable insights into the potential risks businesses may face thus empowering them to prioritize and address the most critical vulnerabilities, ultimately minimizing the likelihood of breaches, data theft, or service disruptions.
Meet Regulatory and Compliance Requirements: Many industries and regulatory bodies require organizations to adhere to specific security standards. Penetration testing is often a mandatory component of these requirements. By conducting regular tests, organizations ensure compliance and mitigate legal risks associated with non-compliance.
Improve Incident Response Capabilities: Penetration testing not only helps identify vulnerabilities but also assesses the effectiveness of incident response processes. By simulating attacks, businesses can evaluate their ability to detect, respond, and mitigate security incidents. This provides an opportunity to refine incident response plans, train staff, and enhance the overall security posture.
Enhance Security Controls: Businesses can evaluate the effectiveness of their existing security controls through pen-testing and can identify gaps or weaknesses in their defense mechanisms. This information helps them fine-tune security controls, apply patches or updates, and implement additional security measures to strengthen their overall security posture.
Save Money: While investing in penetration testing may require resources upfront, it proves to be cost-effective in the long run. Identifying and addressing vulnerabilities before they are exploited by attackers can prevent costly data breaches, financial losses, reputational damage, and potential legal liabilities.
Types of penetration testing
1. Network Penetration Testing
Network penetration testing is the way to assess the security of network infrastructure. Here, skilled ethical hackers attempt to infiltrate the network and expose weaknesses that could potentially be exploited by malicious actors. As a result, your network can be safeguarded from cyberattacks such as DNS level attacks, SSH, Proxy servers, FTP/SMTP, Man in the Middle, etc.
2. Web Application Testing
Web applications are the most common medium to connect with customers, but they are highly vulnerable too, and the prime target of cybercriminals. These applications collect a large volume of personal information of the customers which could be very beneficial for the attackers, thus they often target web applications.
To safeguard these applications, cybersecurity experts perform OWASP (open-source web application security project) penetration testing. OWASP, a standard awareness document, list common types of vulnerabilities faced by applications and supporting systems.
A few vulnerabilities listed in OWASP
- Broken access control
- Cryptographic failures
- Injection attacks
- Insecure design
- Security misconfiguration
- Server-side request forgery
- Identification and authentication failures
- Security logging and monitoring failures, etc.
3. Mobile Application Testing
To protect your app, hire cybersecurity experts for advanced penetration testing. They go beyond basic scans, using real-world expertise and advanced TTPs to identify risks like insecure data storage, untrusted inputs, insufficient cryptography, and code obfuscation.
4. Wireless Network Testing
From smartphones, laptops, and tablets to IoT devices within an organization, every device is connected via wireless networks including wifi and Bluetooth. Data continuously flows in and out of this network thus it needs to be secured from the eyes of hackers. Wireless network penetration testing examines the security loopholes within this network and identifies any weak encryption, insecure configurations, and unauthorized access points that could lead to potential cyberattacks.
5. Social Engineering Testing
Usually, this test is performed on-site and off-site to check the effectiveness of your information security and cybersecurity policies, and how easily an attacker can access the publicly available information. Based on the results, then cyber experts formulate a security awareness training program for the employees to prevent them from social engineering attacks.
6. Physical Penetration Testing
Physical infrastructure, including buildings, data centers, and access control systems is also the target of cybercriminals. They can break into the security mechanisms like locks, alarms, and surveillance systems of an organization’s building. Physical penetrating testing is the way to secure them and quickly address any issues.
7. Client-Side Testing
Client-side penetration testing is the ultimate defense for safeguarding end-user devices. Skilled ethical hackers test desktops, laptops, and mobiles, unearthing vulnerabilities in operating systems, applications, and configurations. They expose hidden gateways that could allow malicious intruders to exploit resources at the client end.
8. Cloud Penetration Testing
Cloud penetration testing helps you evaluate how secure your cloud infrastructure is. It typically considers three main areas i.e., the cloud perimeter, internal cloud environment, and on-premise cloud infrastructure. This penetrating testing type also involves various methods such as transparent box, semitransparent box, and opaque box testing to assess the systems’ weakness.
9. API Penetration Testing
API penetration testing focuses on assessing the security of APIs and identifying vulnerabilities that could be exploited to gain unauthorized access, execute arbitrary code, or manipulate data. Ethical hackers analyze the API endpoints, authentication mechanisms, and input validation, aiming to uncover weaknesses that could compromise the confidentiality or integrity of data exchanged through the API.
Testing Approaches
While implementing the above-mentioned types of penetration testing, it is important to follow these standard approaches:
Black Box: Also known as a blind test, black box testing involves an external attack by ethical hackers who have no prior knowledge of the targeted system. They identify vulnerabilities solely by trial and error.
White Box: Unlike black box testing, the tester has full knowledge of the target system, including architecture, design, and source code in white box testing. This approach mimics an insider threat scenario and helps uncover vulnerabilities that malicious insiders or employees with elevated privileges might exploit. White box testing enables thorough evaluation of specific components or critical areas within the system.
Gray Box: Combining elements of both black box and white box testing, the gray box approach involves partial knowledge of the target system and insight into the internal workings. This method allows organizations to assess vulnerabilities that may arise due to the interaction between different components.
Covert: It is a very highly controlled testing approach as not only penetration testers are unaware of the targeted system, but the internal security teams of an organization are not informed about the covert test. It is also known as a double-blind test because of this reason.
Simply knowing different penetration testing types and approaches are not enough to successfully safeguard the entire organizational infrastructure from cyberattacks. Therefore, testers must be aware of useful penetration testing tools such as Netsparker, Wireshark, Metasploit, and BeEF. The choice depends on the types of system to be tested.
Conclusion
Penetration testing is a powerful cybersecurity practice that empower businesses to navigate the treacherous waters of the digital realm with confidence and resilience without fearing the hackers. However, implementing the different penetration testing types require careful considerations of the testing goals and approach. Professional cybersecurity experts can help you in selection and meeting the safety goals of your business.
Frequently Asked Questions:
Q1. How often should penetration testing be performed?
A: The frequency of penetration testing depends on various factors, such as the organization’s industry, regulatory requirements, and the rate of system changes. Generally, conducting tests annually or after significant system updates are recommended. However, organizations with high-security needs may opt for more frequent assessments.
Q2. Is penetration testing legal?
A: Yes, it is legal when performed with proper authorization from the target organization. Engaging a professional and certified penetration testing service provider ensures compliance with legal and ethical boundaries.
Q3. Can penetration testing cause system downtime or data loss?
A: While penetration testing types carry some risks, professional testers follow strict protocols to minimize the possibility of system disruptions or data loss. By adhering to well-defined rules of engagement and comprehensive planning, they ensure the testing process remains controlled and secure.